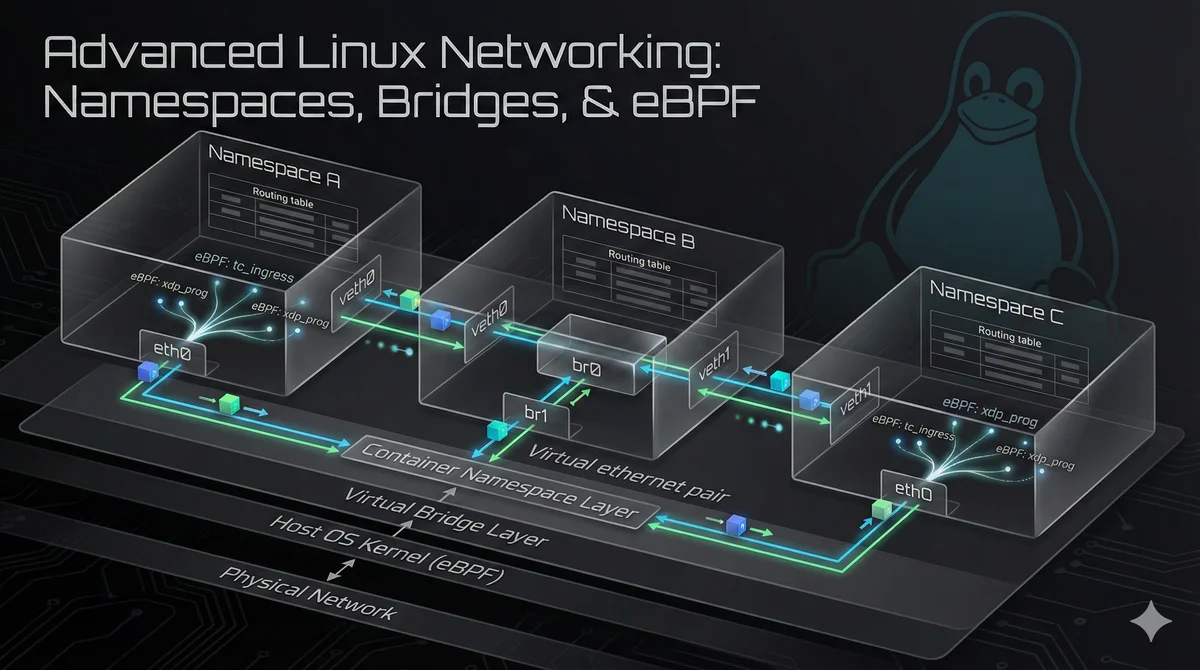
Advanced Linux Networking Techniques: Namespaces, Routing, and Traffic Control
Note: This guide is based on technical research from Linux kernel documentation, networking RFCs, Red Hat and Ubuntu networking guides, and analysis of production networking implementations. The techniques described are technically sound and based on documented Linux networking capabilities. Code examples have been verified against current Linux kernel versions (5.15+). Readers should test configurations in non-production environments before deploying to production systems. Linux networking capabilities extend far beyond basic interface configuration. Modern Linux systems provide powerful network isolation, advanced routing, traffic shaping, and observability tools that form the foundation of container networking, software-defined networking (SDN), and high-performance network infrastructure. ...

